Information security has become a central concern for organizations that store, process, or transmit sensitive data. As cyber threats grow more sophisticated and regulatory requirements become stricter, businesses must adopt structured security frameworks to manage risk effectively.
One of the most widely recognized frameworks for information security management is ISO 27001, an international standard designed to help organizations establish, implement, maintain, and continually improve an Information Security Management System (ISMS).
A key component of this standard is Annex A, which contains a comprehensive set of security controls that organizations can implement to manage and reduce information security risks.
This article explains ISO 27001 Annex A controls, their purpose, how they are structured, and why they play a critical role in building a strong information security framework.
What Are ISO 27001 Annex A Controls?
ISO 27001 Annex A controls are a catalog of security controls that organizations can use to mitigate information security risks identified during risk assessments.
These controls provide practical guidance for implementing security measures that protect data confidentiality, integrity, and availability.
However, it is important to understand that Annex A controls are not mandatory in their entirety. Instead, organizations select the controls that are relevant to their risk environment.
This selection process is documented in the Statement of Applicability (SoA), which explains:
-
Which controls are implemented
-
Which controls are excluded
-
The justification for each decision
In other words, Annex A provides a toolkit of security practices that organizations can adopt based on their security needs.
Structure of ISO 27001 Annex A Controls
In the latest version of the standard, ISO/IEC 27001:2022, Annex A contains 93 controls organized into four main categories.
These categories help organizations address different aspects of information security.
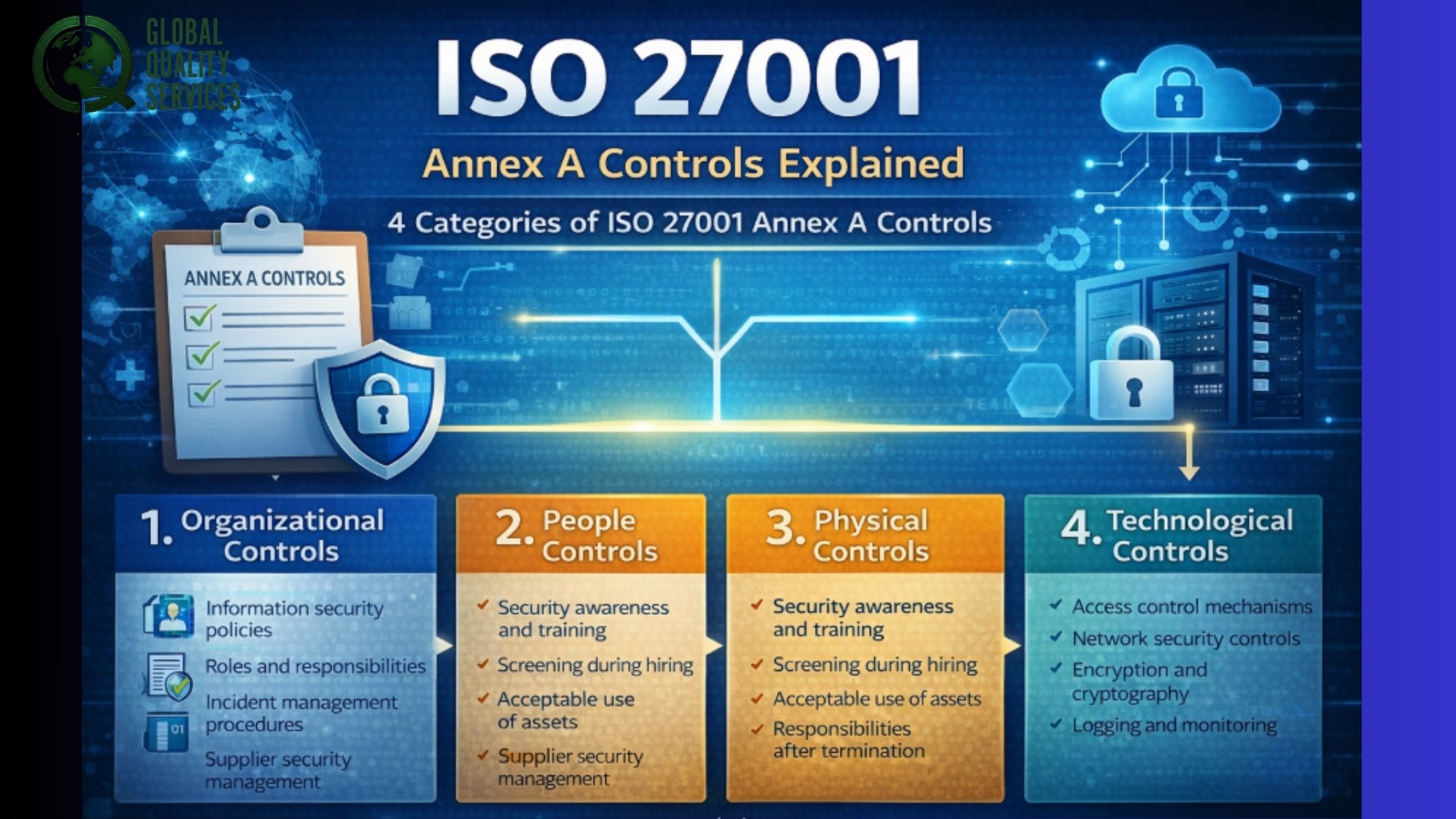
1. Organizational Controls
Organizational controls focus on governance, policies, and management responsibilities related to information security.
These controls help establish a structured approach to managing security risks across the organization.
Examples include:
-
Information security policies
-
Roles and responsibilities for security
-
Supplier security management
-
Incident management procedures
-
Threat intelligence and monitoring
These controls ensure that security is embedded into the organization’s leadership, processes, and decision-making framework.
2. People Controls
People controls address the human factor in information security. Employees, contractors, and third parties can unintentionally introduce security risks, making awareness and accountability essential.
These controls focus on managing risks related to human interaction with information systems.
Examples include:
-
Security awareness and training programs
-
Background verification during hiring
-
Acceptable use of information assets
-
Responsibilities after employment termination
-
Reporting of security incidents
Organizations that implement strong people controls create a security-aware culture where employees understand their role in protecting data.
3. Physical Controls
Physical controls protect the physical infrastructure where information and systems are stored or processed.
Even the most advanced digital security controls can be compromised if attackers gain physical access to systems.
Examples include:
-
Secure entry controls for buildings and server rooms
-
Equipment protection from environmental threats
-
Surveillance systems and monitoring
-
Clean desk and clear screen policies
-
Secure disposal of information assets
Physical security controls help prevent unauthorized individuals from accessing sensitive systems or data.
4. Technological Controls
Technological controls address the technical aspects of information security, including system protection, network security, and access management.
These controls are typically implemented through IT infrastructure, security tools, and system configurations.
Examples include:
-
Access control mechanisms
-
Network security controls
-
Encryption and cryptographic protections
-
Malware protection systems
-
Logging and monitoring mechanisms
Technological controls form the technical backbone of an organization’s cybersecurity posture.
Key Examples of ISO 27001 Annex A Controls
To understand how Annex A works in practice, it is helpful to look at some commonly implemented controls.
Access Control Management
Access control ensures that only authorized individuals can access specific information or systems.
This includes measures such as:
-
User authentication
-
Role-based access control
-
Privileged access management
-
Multi-factor authentication
Proper access control prevents unauthorized access to sensitive information.
Information Security Policies
Information security policies establish clear guidelines for how security should be managed within the organization.
These policies typically define:
-
Acceptable use of company systems
-
Data handling procedures
-
Security responsibilities for employees
-
Incident response procedures
Policies provide the foundation for consistent security practices across the organization.
Incident Management
No security system is completely immune to threats. Incident management controls ensure organizations can detect, respond to, and recover from security incidents effectively.
Key components include:
-
Incident reporting procedures
-
Investigation processes
-
Communication plans
-
Post-incident review
Effective incident management minimizes damage and supports continuous improvement.
Cryptographic Controls
Cryptography protects sensitive information from unauthorized access during storage and transmission.
Examples include:
-
Encryption of sensitive data
-
Secure key management
-
Use of approved cryptographic algorithms
These controls ensure that even if data is intercepted, it remains unreadable without proper authorization.
Supplier Security Management
Organizations increasingly rely on third-party vendors and service providers. Supplier security controls help ensure that external partners maintain appropriate security standards.
This may include:
-
Security requirements in contracts
-
Vendor risk assessments
-
Monitoring supplier compliance
Managing third-party risk is critical because supply chain vulnerabilities are a common source of security incidents.
Why Annex A Controls Are Important
ISO 27001 Annex A controls provide several important benefits for organizations.
Risk-Based Security
Annex A controls support a risk-based approach to security management. Instead of applying generic security practices, organizations implement controls tailored to their specific risks.
This ensures resources are used efficiently while maintaining strong protection.
Compliance with Regulations
Many data protection regulations require organizations to demonstrate strong information security practices.
Implementing ISO 27001 Annex A controls can help support compliance with regulations such as:
-
GDPR
-
HIPAA
-
Data protection laws in various jurisdictions
These controls provide a recognized framework for demonstrating due diligence in protecting information.
Stronger Cybersecurity Posture
By implementing a structured set of security controls, organizations can significantly reduce their exposure to cyber threats.
Annex A helps address common risks such as:
-
Unauthorized access
-
Data breaches
-
Insider threats
-
Malware attacks
This strengthens the organization’s overall cybersecurity posture.
Improved Customer Trust
Certification against ISO 27001 demonstrates that an organization follows internationally recognized security standards.
For clients, partners, and regulators, this certification signals that information security is managed systematically and responsibly. As a result, ISO 27001 often becomes a competitive advantage, especially when dealing with sensitive data or enterprise clients.
How Organizations Implement Annex A Controls
Implementing ISO 27001 Annex A controls typically follows several steps.
1. Conduct a Risk Assessment
Organizations begin by identifying information assets and evaluating potential security risks.
This process determines which controls are necessary.
2. Select Applicable Controls
Based on the risk assessment, organizations select relevant Annex A controls. These selections are documented in the Statement of Applicability (SoA).
3. Implement Security Measures
Selected controls are implemented through:
-
Policies and procedures
-
Technical safeguards
-
Employee training
-
Physical security measures
4. Monitor and Review Controls
Information security is not a one-time activity.
Organizations must continuously monitor controls through:
-
Internal audits
-
security monitoring
-
management reviews
5. Continuous Improvement
ISO 27001 requires ongoing improvement of the ISMS. Organizations regularly update controls to address new threats, business changes, or regulatory updates.
Conclusion
ISO 27001 Annex A controls provide a structured framework for managing information security risks across an organization. By offering a comprehensive set of organizational, people, physical, and technological controls, Annex A helps businesses implement practical safeguards that protect sensitive information.
Rather than prescribing a rigid checklist, the standard promotes a risk-based approach, allowing organizations to choose controls that align with their specific security environment.
When implemented effectively, Annex A controls strengthen cybersecurity defenses, support regulatory compliance, and build trust with customers and partners.
For organizations aiming to establish a mature information security program, understanding and applying ISO 27001 Annex A controls is a critical step toward achieving a resilient and compliant security posture. Connect with Global Quality Services team to know more.